PKI & TLS — For the moments that matter
Free, vendor-neutral resources for engineers and teams managing certificates in the real world.
Learn By Doing
Interactive visualizations that make complex concepts click

SSL/TLS Diagnostic Troubleshooter
Diagnose SSL/TLS connection problems systematically. Interactive troubleshooter for common issues.
Try it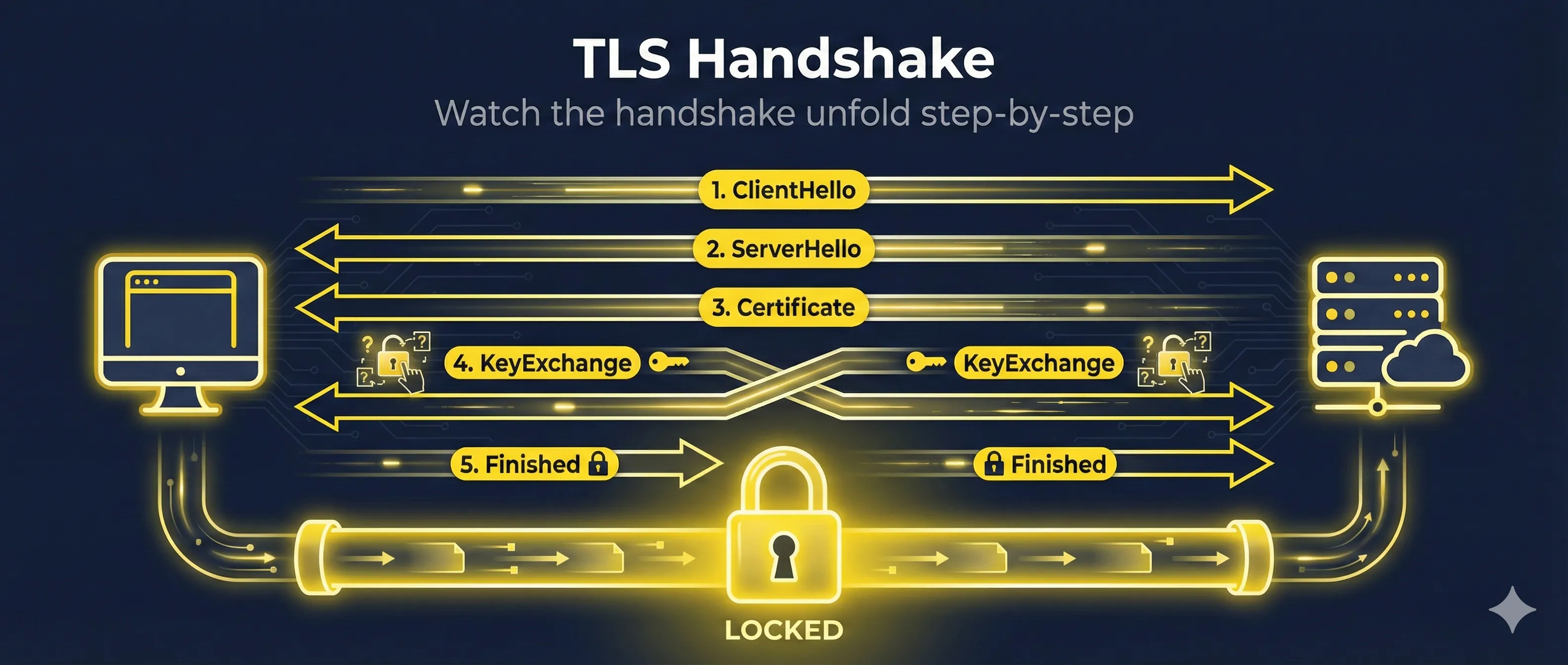
TLS Handshake Step-by-Step
Step through the TLS 1.2 and 1.3 handshake message by message. See ClientHello, ServerHello, and more.
Try it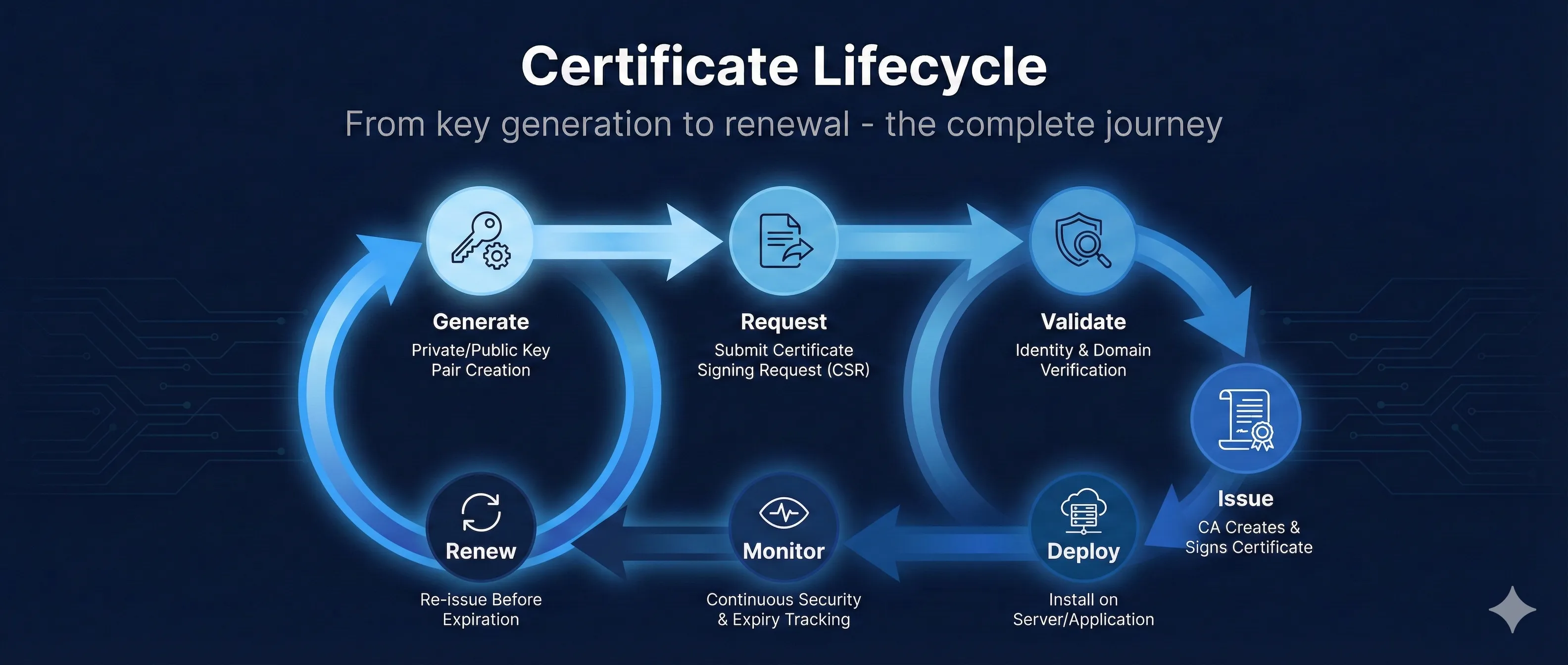
Certificate Lifecycle Management
Walk through the complete certificate lifecycle from key generation to CSR, issuance, deployment, monitoring, and renewal.
Try itGo Deeper
In-depth guides for real-world PKI challenges

The 47-Day Certificate Timeline
Complete timeline of CA/Browser Forum Ballot SC-081v3 reducing TLS certificate validity from 398 to 47 days by 2029. Live countdowns, phase breakdowns, and action items.
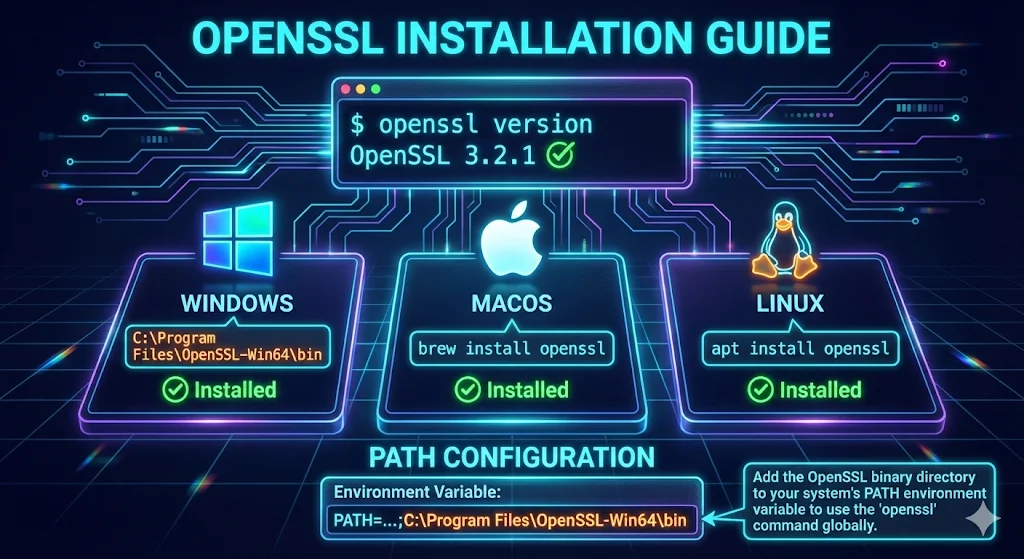
How to Install OpenSSL
Install OpenSSL on Windows, Mac, and Linux. Step-by-step with PATH configuration and verification.
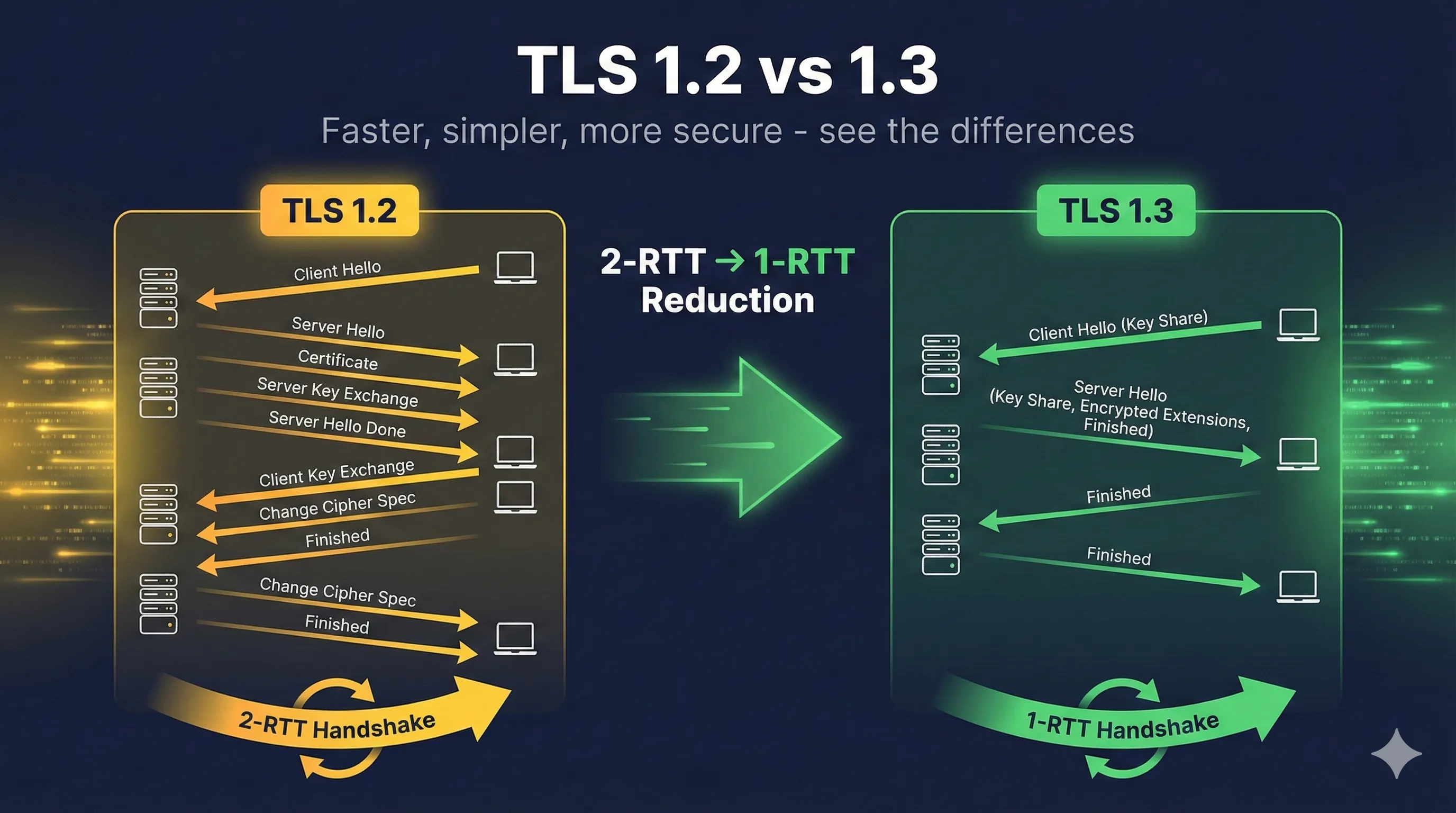
TLS 1.2 vs 1.3
Compare TLS versions side-by-side. See why TLS 1.3 is faster and more secure.
Trusted By the Community
 PKI ConsortiumMember
PKI ConsortiumMember Practical NetworkingAffiliate Partner (Ed Harmoush)
Practical NetworkingAffiliate Partner (Ed Harmoush) HID GlobalReseller Partner
HID GlobalReseller Partner ZeroSSLAffiliate Partner
ZeroSSLAffiliate PartnerLevel Up Your PKI Skills
Practical Tools for Real Situations
From active troubleshooting to audit prep — start where you need to